Showing posts with label computer crime. Show all posts
Showing posts with label computer crime. Show all posts
Wednesday, April 24, 2013
Recently patched Java flaw already targeted in mass attacks, researchers say
PCWorld - A recently patched Java remote code execution vulnerability is already being exploited by cybercriminals in mass attacks to infect computers with scareware, security researchers warn.
The vulnerability, identified as CVE-2013-2423, was one of the 42 security issues fixed in Java 7 Update 21 that was released by Oracle on April 16.
According to Oracle’s advisory at the time, the vulnerability only affects client, not server, deployments of Java. The company gave the flaw’s impact a 4.3 out of 10 rating using the Common Vulnerability Scoring System (CVSS) and added that “this vulnerability can be exploited only through untrusted Java Web Start applications and untrusted Java applets.”
However, it seems that the low CVSS score didn’t stop cybercriminals from targeting the vulnerability. An exploit for CVE-2013-2423 was integrated into a high-end Web attack toolkit known as Cool Exploit Kit and is used to install a piece of malware called Reveton, an independent malware researcher known online as Kafeine said Tuesday in a blog post.
More
Labels:
computer crime,
computer security,
hackers,
java flaw,
mass attacks,
recently patched,
researchers,
safe computing,
targeted,
tech news
Wednesday, April 18, 2012
You Got Hacked! What Now?

PCMag.Com - The phone rings. It’s your sweetheart, in tears. Why, oh why, did you change your status on Facebook to Single? Are you moving to Dubuque? Facebook says you live in Dubuque.
First things first; offer all necessary reassurance that you’re not breaking up and moving away. Then face the facts—you’ve been hacked.
The evidence might come out in other ways. Your friends may ask why you sent them that stupid email ad for Viagra. You may find one day that you simply can’t log in to your email or social media account. It’s an awful feeling, but you can recover.
How Did It Happen?
It’s conceivable that a cyber-criminal mastermind targeted you personally for a hack attack. A “spear-phishing” email message specially crafted using your personal information might have tricked you into connecting with a malicious site. Or perhaps an active hacker in some Moscow basement exploited a vulnerability in your OS.
Yes, these scenarios are conceivable, but they’re almost inexpressibly unlikely. You’re special, of course, but you’re not that special. It’s much more likely that you just weren’t careful, or weren’t lucky. Perhaps you logged in to your email from a public computer without taking proper precautions. Maybe you shared your password with a friend who’s turned out not to be such a friend after all. A valid website that’s been compromised by injected malware can infest your system with a data-stealing Trojan, and that doesn’t require any personal attention from cyber-spies. More
Labels:
computer crime,
computer security,
cyber crime,
hackers,
hacking,
tech news
Monday, April 2, 2012
The Future is Now – The Dark Side and Hacktivism

TechNewsWorld - Understand that the Dark Side is greatly motivated by social and political interests that are difficult to predict and not necessarily useful in forming strategic or tactical defense plans. This understanding will help organizations craft strategic decisions about layered protections in all verticals exposed to the Internet.
We live in times when technology is exceeding the understanding of educational institutions and corporations. A highly social Web and a bad economy is making the Dark Side — the Internet underworld where cybercrime and hacking run rampant — overwhelming.
Hacktivism is the new, hip thing; it has become a hobby for people with higher-than-average computer knowledge. The movement is led by an elite few who have a deep, lifelong knowledge of computers, and it includes senior Fortune 100 corporate executives and highly placed governmental employees, as well as the ranks of the unemployed.
The elite world of hacktivism is at the center of the Internet’s Dark Side. While governmental agencies are looking for the individuals responsible for various acts of hacktivism, they struggle with using their tried-and-true methods to move up the food chain to identify hacktivist leaders.
What is not well understood is that these layers cannot be penetrated by the standard law enforcement methods that were once effective in collapsing organized crime groups.
Hacktivism exists because the Internet is an open society that has no boundaries in which normal legal process can be applied without taking significant and draconian action, like direct control of the systems that keep the Internet alive. The traditional legal requirements for evidence are hampered by the very void in which the elites live. More
Labels:
activism,
computer crime,
cyber crime,
dark side,
hackers,
hackivism,
tech news
Wednesday, February 22, 2012
Why Anonymous is Winning Its War on Internet Infrastructure

“To our hacker allies, our fellow occupiers, our militant comrades all over the world, the time for talk is over: it’s time to hack and smash, beat and shag.”
Forbes - The call to arms issued last week by the international hacker group Anonymous was accompanied by a frenzy of online hacking. Attackers took down the websites of a tear-gas manufacturer in Pennsylvania, the Nasdaq and BATS stock exchanges and the Chicago Board Options Exchange. A few days later they hacked into websites owned by the Federal Trade Commission and the Bureau of Consumer Protection.
The messages they left behind—about their opposition to everything from the Anti-Counterfeiting Trade Agreement, a controversial new treaty for enforcing intellectual property rights, to violent suppression of democracy protestors in the Middle East—had the air of giddy jubilation.
“Guess what? We’re back for round two,” the hackers wrote in reference to their attack on the FTC websites, their second such raid on the agency in less than a month. “With the doomsday clock ticking down on Internet freedom, Antisec has leapt into action. Again. Holy deja vu hack Batman! Expect us yet?”
Comic posturing aside, the hackers seemed amazed by their success: A barely organized ragtag “team of mayhem,” as one Anonymous offshoot dubbed itself, was knocking down the Web infrastructure built by major corporations and large government agencies as if it were nothing but paper backdrops in a school play. More
Labels:
anonymous,
business news,
computer crime,
cyber crime,
hackers,
hacktivists,
internet infrastructure,
tech news,
winning
Wednesday, January 25, 2012
Hackers Breached Railway Network, Disrupted Service

Hackers
attacked computers at an an unidentified railway
company, disrupting
railway signals for two days in
December, according to a government memo
obtained
by Nextgov.
by Nextgov.
An investigation determined that hackers — possibly from overseas — had penetrated the system from three IP addresses, according to the memo, which did not name the country from which the hack occurred.
“Some of the possible causes lead to consideration of an overseas cyberattack,” the memo said.
Information stating that a targeted attack occurred was sent out on Dec. 5, along with alerts listing the three IP addresses, to several hundred railroad firms and public transportation agencies, in addition to unnamed partners in Canada.
A DHS spokesman acknowledged the breach in a statement to Threat Level.
“On December 1, a Pacific Northwest transportation entity reported that a potential cyber incident could affect train service,” said spokesman Peter Boogard in a statement. “The Department of Homeland Security (DHS), the FBI and our federal partners remained in communication with representatives from the transportation entity in support of their mitigation activities and with state and local government officials to send alerts to notify the transportation community of the anomalous activity as it was occurring.”
A DHS official added that after more in-depth analysis of the incident, it did not appear to be a targeted attack aimed at the railway and halting service, but was more of a random incident that simply hit the transportation entity. He would not elaborate. More
Labels:
breach,
computer crime,
cyber crime,
hackers,
railway network,
tech news
Monday, January 23, 2012
Anonymous Tricks Bystanders Into Attacking Justice Department
A version of Anonymous’ voluntary botnet software, known as LOIC (Low Orbit Ion Canon), was modified to make it not so voluntary, drafting unwary bystanders, journalists and even anons who don’t support DDoS tactics into attacks on the U.S. Justice Department. Thursday’s trickery seems not to have been central to the successful takedown of sites like justice.gov, RIAA.com and MPAA.com, but not all anons are pleased with forcing unwitting bystanders to join in a potentially illegal action.
The trick snagged those who happened to click on a shortened link on social-media services, expecting information on the ongoing #opmegaupload retaliation for the U.S. Justice Department’s takedown of popular file sharing site Megaupload. Instead they were greeted by a Javascript version of LOIC — already firing packets at targeted websites by the time their page was loaded.
Several anons speaking to Wired on condition of anonymity voiced dismay that a tactic they consider to be the modern-day equivalent of a sit-in (denial-of-service attacks leave no lasting damage) was ethically corrupted by the new version.
“Preying on unsuspecting users is despicable,” said one anon, speaking to Wired in an online chat. “We need to fight for the user, not potentially land them in jail.”
As part of Thursday’s raging reaction from Anonymous to the Megaupload arrests, people by the thousands voluntarily pointed the LOIC at targets like FBI.gov, DOJ.gov, MPAA.org, BMI.org, RIAA.org and copyright.gov, part of an effort that knocked these sites offline for parts of the day. The tool bombards a targeted site with traffic, in hopes of overwhelming servers so that no one can visit the site. More
Labels:
anonymous,
bystanders,
computer crime,
computer security,
department of justice,
DOJ,
hackers,
hacktivists,
tech news,
tricks
Friday, January 20, 2012
Anonymous Hackers Hit DOJ, FBI, Universal Music, MPAA And RIAA After MegaUpload Takedown

Just minutes after the U.S. Department of Justice repossessed the domains of Megaupload, Megavideo, Megaporn and a collection of other popular filesharing sites, the hacker collective Anonymous got to work on a few takedowns of its own.
On Thursday afternoon, Anonymous claimed credit for cyberattacks that knocked offline the websites of the U.S. Department of Justice, Recording Industry of America, Motion Picture Association of America and Universal Music. The so-called denial of service attacks that overwhelmed those sites with junk traffic came less than an hour after the Justice Department announced the takedown of the Mega sites, along with the arrest of former hacker and Mega founder Kim Dotcom and six others, who are being indicted on charges of copyright infringement and money laundering.
“One thing is certain: EXPECT US!,” wrote the Anonymous-linked Anonops Twitter feed Thursday just after the Mega raid, adding a hashtag for Megaupload.
“Anonymous/Megaupload backlash update: http://RIAA.ORG is now Tango Down,” wrote the Twitter feed Anonnews less than one hour later, as other Anonymous feeds claimed credit for downing Justice.gov and Universalmusic.com.
Update: The U.S. Copyright office website is now down as well. Expect this to go on for a while. “Get some popcorn… it’s going to be a long lulzy night,” writes Anonnews. More
Labels:
anonymous,
business news,
computer crime,
DOJ,
fbi,
hackers,
hacktivists,
megaupload,
MPAA And RIAA,
tech news,
Universal Music
Friday, December 30, 2011
Hackers to exploit vulnerable infrastructure in 2012, McAfee warns

Attackers will increasingly leverage the lack of cybersecurity preparedness of utilities and other critical infrastructure in 2012, predicts McAfee Labs.
Many of the environments where supervisory control and data acquisition (SCADA) systems are deployed do not have stringent security practices, noted McAfee’s 2012 Threat Predictions report.
“There are a lot of different people looking at infrastructure, SCADA, utilities, energy. It’s an area that we think is going to be a big deal in 2012….What you are looking at is unpreparedness”, said Dave Marcus, director of research and communications at McAfee Labs.
Marcus told Infosecurity that the “most fascinating thing” about the Duqu attack against industrial systems was that it used rogue certificates. “That is a big deal, because it undermines the trust in secure socket layers and secure website communication; if you are going to generate rogue keys and fake certificates, that undermines the underlying trust in the operating system”, he said.
Duqu also demonstrated advancements in rootkits, Marcus noted. “We are seeing a lot more targeting of lower layers of the operating system. We think we will see more hardware and BIOS [basis input/output system] targeting, and even targeting of the master boot record….Duqu had a lot of that stealth rootkit activity.”
In its report on Duqu, Symantec judged that it is “essentially the precursor to a future Stuxnet-like attack” against industrial control systems. These systems are used to control everything from nuclear power plants and the electricity grid to oil pipelines and large communication systems. More
Labels:
2012,
computer crime,
computer security,
exploit,
hackers,
mcafee,
tech news,
vulnerable infrastructure
Tuesday, December 6, 2011
Top Hacker Disasters of 2011: Five Critical Lessons for Businesses
Fox Business - This year is already being called “The Year of the Hack,” due to the unprecedented number of damaging attacks against major companies like Sony, RSA Security, Google (GOOG: 624.82, -0.83, -0.13%) and even the U.S. government. It’s hard to remember a time when businesses faced as many online threats as they do today.
From hacktivist groups like Anonymous, corporate and state-sponsored cyber espionage and organized crime and rogue hackers, every business, regardless of its size, is finding itself in the cross hairs of cyber attacks.
Why is so much hacking happening now? The answer is simple: More valuable information is stored online now than ever before, and at the same time, many companies have been lax about IT security.
Most of this year’s high-profile attacks should have been prevented. It’s the job of every business owner to learn valuable lessons about why these companies were hacked and how they could have prevented it.
Here is a recap of 2011’s significant hacks with important tips for businesses:
RSA Security, hacked in March 2011:
RSA, best known for its SecurID tokens, was severely jeopardized by a clever cyber attack earlier this year. The attackers used social engineering (just another term for “con”) to trick RSA employees into opening a spoofed, or fake, email and downloading an infected Excel spreadsheet. This attack gave the hackers access to the computer network and from there, they stole SecurID tokens and used them to hack military contractors.
Key Lesson No.1: Protect Critical Data. RSA should not have had its SecurID token secrets online. What valuable information does your business store in online databases? Many executives don’t know, and classifying business data should be near the top of their chief information security officer’s (CISO) to-do list. Business owners should thoroughly examine the information they store online and store critical data offline or behind strict network segmentation.
Key Lesson No.2: Segment Your Network. The attack on RSA used employees to get inside the company. Employee training isn’t reliable, therefore it’s more important for businesses to safeguard their network by segmenting the network so if one employee’s PC is infected it can’t spread laterally through the entire system.
Sony, hacked April to June 2011
The attack on Sony made news for weeks as the company was attacked by LulzSec and the Playstation network shut down. All told, the damage to Sony from these attacks reportedly more than $170 million. More
Labels:
business news,
computer crime,
cyber crime,
hacker disasters,
hackers,
lessons learned,
tech news,
top hacker disasters of 2011
Friday, September 16, 2011
Free Internet Security for Small Businesses

PCWorld - Are you looking to cut expenses for your small business or organization? You can save some cash by replacing those annual antivirus subscriptions with free equivalents. Though most free tools are restricted to home or personal use, a few are also available for businesses at no charge. We’ll look at what the various freebies offer, and explain how to get started using them.
For Protection Against Multiple Malware Threats: Comodo Internet Security
Comodo Internet Security (CIS) provides a sturdy package for blocking viruses, spyware, rootkits, botnets, worms, and other malware.CIS goes beyond the basic malware protection that you get with a lot of freebies, offering a built-in firewall to guard against hackers and intrusions. Windows comes with a free native firewall, but using CIS’s third-party alternative provides more-advanced configuration options. In addition its consistent interface is useful if different versions of Windows run on your network, since the native firewall differs from one Windows version to another.
When we reviewed Comodo’s free product in late 2010, we liked how well it blocked new malware, though we found that it had a few drawbacks in other respects. Still, it managed a an overall rating of 3.5 stars–a solid mark.
The program’s Defense+ feature analyzes and manages executable files to protect critical system files and to prevent malware from causing harm. It also has automatic sandbox functionality, which runs unknown files in an isolated environment so they can’t do any damage if they turn out to contain malware.
Comodo’s SecureDNS service conducts malicious-website filtering to block phishing, malware-carrying sites, and other known dangerous websites before they can infect you. This DNS-based service is similar to OpenDNS, which we’ll discuss later.
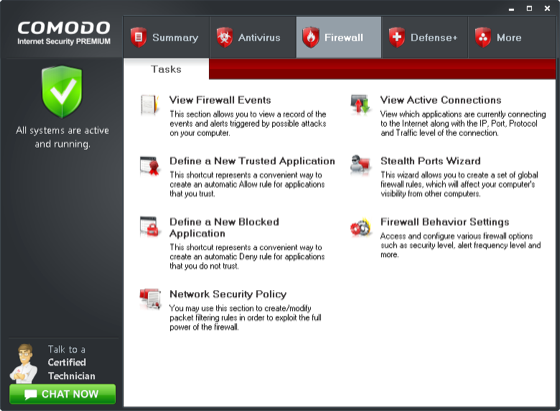
Unlike many free antivirus products, Comodo Internet Security (CIS) offers a firewall component.
CIS lets you adjust an array of advanced settings governing heuristics levels and other general scanning settings, as well as customizable “scanning profiles.” The Firewall and Defense+ features are highly customizable, too. You can fine-tune the protection by using rules, policies, definitions of trusted files/networks, and other settings.
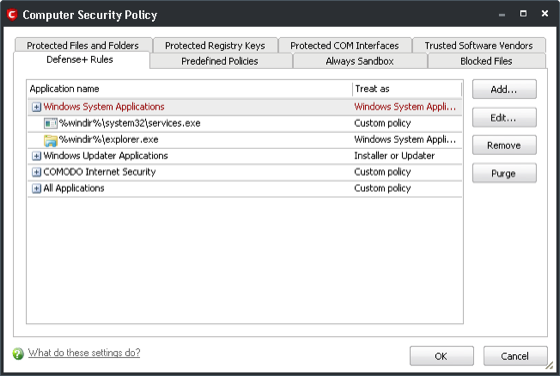
Comodo Internet Security’s Computer Security Policy manager.
CIS’s configuration management is very convenient for running on multiple PCs. Just configure one PC, export the configuration file, and import it to the others. All settings are backed up, including scanning profiles, security policies, and password protection.
If you want to give CIS a try, download it from the Comodo site. Just prior to installing it, make sure that you have completely uninstalled any existing antivirus program and rebooted Windows to prevent any conflicts. You should also disable Windows Firewall if you choose to install Comodo Firewall when installing CIS. During the installation, the setup program will ask you whether you want to enable SecureDNS. If you plan on using OpenDNS (discussed later), don’t enable SecureDNS.
Once you’ve installed CIS, go through all of the screens and settings, and configure it to your liking. The default settings are best for most situations; for full protection, however, you may want to consider enabling cloud scanning and rootkit scanning in the Scanner Settings of the Antivirus component. Also, discover and configure the security policies settings of the Firewall and Defense+ components.
To reduce unnecessary Internet traffic when you use CIS on multiple PCs, install the Comodo Offline Updater (available at no charge from Comodo’s site) to one PC, so that it can download Comodo’s virus database updates. Then configure each of the other CIS installations on your network to check for updates from that PC instead of from the Comodo server.
To change the update server that CIS checks, select the More tab, click Preferences, and select the Update tab. Then add to the list the IP address or host name of the PC that you installed the Comodo Offline Updater on. Consider keeping the Comodo server enabled but in the number two position, in case you encounter a problem with your PC.
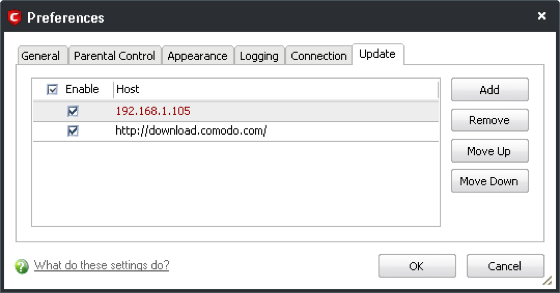
Changing the update server used to download virus signatures.You should also consider setting a password for CIS and locking down the configuration so that other users can’t change any settings. To do this, open CIS, select the More tab, click Preferences, and select the Parental Control tab.
Next: Microsoft Security Essentials and OpenDNS…
Labels:
business news,
computer crime,
cyber crime,
free internet security,
hackers,
internet security,
malware,
small business internet security,
tech news
Thursday, September 1, 2011
Energy Grid: Safe From Cyber Attack?

Towers carrying electrical lines in San Francisco, Calif. The smart grid that overlays power systems may be vulnerable to cyber attacks. Click to enlarge this image. Getty Images
THE GIST
- The smart grid promises more efficient energy use but may be more vulnerable to attacks.
- The nation’s electric utilities are now catching up when it comes to protecting the grid.
- Some cyber attacks on the grid have already occurred.
Discovery News - As the 9/11 anniversary approaches, experts wonder if the United States could withstand a breach of its power network, or whether the so-called “smart grid,” which promises more efficient energy use, is more vulnerable to cyber attacks than the old one. The answers are yes and yes.
When it comes to protecting against hackers, the nation’s electric utilities are about where the financial and telecommunications industries were a decade ago, according to Andy Bochman, Energy Security Lead for IBM’s Rational division, which focuses on smart-grid security software.
Bochman says the electrical sector has been late in the game when it comes to embracing information technology that focuses on security, but is catching up.
NEWS: Cyber-Security System Mimics Human Immune Response
“We are now at a sustained back-and-forth between the powers that are trying to attack these systems, and forces aligned to defend them,” Bochman said.
While that statement may sound a bit like a sci-fi plot, the reality is that utilities across the country have seen a big increase in deliberate attacks, as well as inadvertent screw-ups that have thrown thousands of customers into the dark.
In a study released in April of electrical utilities by McAfee, the computer security firm, and the Center for Strategy and International Studies in Washington, utility industry executives from 14 nations found that things are getting worse.
DNEWS VIDEO: A hacker explains why hacking isn’t the same thing as cyber crime.
“One of the more startling results of our research is the discovery of the constant probing and assault faced by these crucial utility networks. Some electric companies report thousands of probes every month. Our survey data lend support to anecdotal reporting that militaries in several countries have done reconnaissance and planning for cyberattacks on other nations’ power grids, mapping the underlying network infrastructure and locating vulnerabilities for future attack,” the report stated.
Could a Stuxnet-type virus, which pretty much destroyed one of Iran’s nuclear power plants, happen in the United States? Some similar, but less dangerous events, already have:
•In April 2009, The Wall Street Journal reported that that cyber spies had infiltrated the U.S. electric grid and left behind software that could be used to disrupt the system. The hackers came from China, Russia and other nations and were on a fishing expedition to map out the system, the paper reported. More
When it comes to protecting against hackers, the nation’s electric utilities are about where the financial and telecommunications industries were a decade ago, according to Andy Bochman, Energy Security Lead for IBM’s Rational division, which focuses on smart-grid security software.
Bochman says the electrical sector has been late in the game when it comes to embracing information technology that focuses on security, but is catching up.
NEWS: Cyber-Security System Mimics Human Immune Response
“We are now at a sustained back-and-forth between the powers that are trying to attack these systems, and forces aligned to defend them,” Bochman said.
While that statement may sound a bit like a sci-fi plot, the reality is that utilities across the country have seen a big increase in deliberate attacks, as well as inadvertent screw-ups that have thrown thousands of customers into the dark.
In a study released in April of electrical utilities by McAfee, the computer security firm, and the Center for Strategy and International Studies in Washington, utility industry executives from 14 nations found that things are getting worse.
DNEWS VIDEO: A hacker explains why hacking isn’t the same thing as cyber crime.
“One of the more startling results of our research is the discovery of the constant probing and assault faced by these crucial utility networks. Some electric companies report thousands of probes every month. Our survey data lend support to anecdotal reporting that militaries in several countries have done reconnaissance and planning for cyberattacks on other nations’ power grids, mapping the underlying network infrastructure and locating vulnerabilities for future attack,” the report stated.
Could a Stuxnet-type virus, which pretty much destroyed one of Iran’s nuclear power plants, happen in the United States? Some similar, but less dangerous events, already have:
•In April 2009, The Wall Street Journal reported that that cyber spies had infiltrated the U.S. electric grid and left behind software that could be used to disrupt the system. The hackers came from China, Russia and other nations and were on a fishing expedition to map out the system, the paper reported. More
Labels:
computer crime,
cyber attack,
cyber crime,
energy grid,
tech news,
u.s. news
Monday, August 22, 2011
Advanced Encryption Standard cracked - AES secures most online transactions & wireless communications
h/t - @FurryStoat
Boffins from Microsoft and the Katholieke Universiteit Leuven in Belgium have cracked the Advanced Encryption Standard (AES), the encryption algorithm.
AES is used to secure most all online transactions and wireless communications so breaking the system is bad news for anything dependant on it.
Their method can recover an AES secret key from three to five times faster than previously thought possible and do not need to assume related-keys.
"Most of our attacks only need a very small part of the codebook and have small memory requirements, and are practically verified to a large extent. As our attacks are of high computational complexity, they do not threaten the practical use of AES in any way," the report said. More
Labels:
advanced encryption standard cracked,
aes,
computer crime,
computer security,
cyber crime,
hacking,
microsoft,
tech news
Wednesday, August 10, 2011
Friday, August 5, 2011
Web malware more than doubled in the second quarter
The rate of unique web malware more than doubled in the second quarter, from 105,536 unique encounters of web malware in March 2011 to 287,298 unique encounters in June 2011, according to Cisco’s latest quarterly threat report.
Infosecurity.Com - The average web malware encounter rate in the second quarter was 335 encounters per enterprise per month, with the highest peaks in March (455) and April (453), according to Cisco's second-quarter threat report.
From an encounter-per-seat perspective, companies with 5001 to 10,000 employees and companies with more than 25,000 employees experienced significantly higher malware encounters compared to other size segments.
Despite the increase in web malware encounters, the number of unique malware hosts and unique IP addresses remained relatively consistent between March 2011 and June 2011, the report noted.
Brute-force SQL login attempts increased significantly during the second quarter, coinciding with increased reports of SQL injection attacks and other brute force intrusions – resulting in an increase in data breaches throughout the period. More
Labels:
cisco,
computer crime,
computer security,
cyber crime,
doubled in second quarter,
malware,
tech news
Widespread Hijacking of Search Traffic in the United States

Earlier this year, two research papers reported the observation of strange phenomena in the Domain Name System (DNS) at several US ISPs. On these ISPs' networks, some or all traffic to major search engines, including Bing, Yahoo! and (sometimes) Google, is being directed to mysterious third party proxies.
A report in New Scientist today documents that the traffic is being rerouted through a company called Paxfire. This blog post, coauthored with one of the teams that discovered the phenomenon, will explain the situation in more detail.
Who is rerouting this search traffic?
The published research papers did not identify the controller of the proxy servers that were receiving the traffic, but parallel investigations by the ICSI Networking Group and EFF have since revealed a company called Paxfire as the main actor behind this interception. Paxfire's privacy policy says that it may retain copies of users' "queries", a vague term that could be construed to mean either the domain names that they look up or the searches they conduct, or both. The redirections mostly occur transparently to the user and few if any of the affected ISP customers are likely to have ever heard of Paxfire, let alone consented to this collection of their communications with search engines.The proxies in question are operated either directly by Paxfire, or by the ISPs using web proxies provided by Paxfire. Major users of the Paxfire system include Cavalier, Cogent, Frontier, Fuse, DirecPC, RCN, and Wide Open West. Charter also used Paxfire in the past, but appears to have discontinued this practice.
Why do they do this?
In short, the purpose appears to be monetization of users' searches. ICSI Networking's investigation has revealed that Paxfire's HTTP proxies selectively siphon search requests out of the proxied traffic flows and redirect them through one or more affiliate marketing programs, presumably resulting in commission payments to Paxfire and the ISPs involved. The affiliate programs involved include Commission Junction, the Google Affiliate Network, LinkShare, and Ask.com. When looking up brand names such as "apple", "dell", "groupon", and "wsj", the affiliate programs direct the queries to the corresponding brands' websites or to search assistance pages instead of providing the intended search engine results page.What can I do about it?
If you want to know if the network you're currently on is subject to this type of traffic redirection, you can run a Netalyzr test. And the best protection against the privacy and security risks created by this type of hijacking is to visit sites using HTTPS rather than HTTP, which can easily be achieved using EFF's HTTPS Everywhere Firefox extension.More technical details below...
A detailed explanation
For most users of the World Wide Web, visiting a website equals clicking on a link to the site or entering the site's name into their browser, and receiving the corresponding page from the site. Users generally assume that the site's name is identical to the site itself, and essentially trust the site's authenticity if it looks as usual and the browser does not pop up phishing warnings or other signs of trouble. Paxfire's misdirection of search traffic undermines this trust. More
Labels:
computer crime,
cyber crime,
fbi arrests 16 in anonymous hacking,
hijacking of search traffic,
tech news
Monday, August 1, 2011
Researchers Say Vulnerabilities Could Let Hackers Spring Prisoners From Cells

Wired - Vulnerabilities in electronic systems that control prison doors could allow hackers or others to spring prisoners from their jail cells, according to researchers.
Some of the same vulnerabilities that the Stuxnet superworm used to sabotage centrifuges at a nuclear plant in Iran exist in the country’s top high-security prisons, according to security consultant and engineer John Strauchs, who plans to discuss the issue and demonstrate an exploit against the systems at the DefCon hacker conference next week in Las Vegas.
Strauchs, who says he engineered or consulted on electronic security systems in more than 100 prisons, courthouses and police stations throughout the U.S. — including eight maximum-security prisons — says the prisons use programmable logic controllers to control locks on cells and other facility doors and gates. PLCs are the same devices that Stuxnet exploited to attack centrifuges in Iran.
“Most people don’t know how a prison or jail is designed, that’s why no one has ever paid attention to it,” says Strauchs. “How many people know they’re built with the same kind of PLC used in centrifuges?”

Diagram showing the typical parts of a PLC used for door-control systems. Image courtesy of Teague Newman
Though Siemens PLCs are used in some prisons, they’re a relatively small player in that market, Strauchs says. The more significant suppliers of PLCs to prisons are Allen-Bradley, Square D, GE and Mitsubishi. Across the U.S. there are about 117 federal correctional facilities, 1,700 prisons, and more than 3,000 jails. All but the smallest facilities, according to Strauchs, use PLCs to control doors and manage their security systems.
Strauchs, who lists a stint as a former CIA operations officer on his bio, became interested in testing PLCs after hearing about the systems Stuxnet targeted and realizing that he had installed similar systems in prisons years ago. He, along with his daughter Tiffany Rad, president of ELCnetworks, and independent researcher Teague Newman, purchased a Siemens PLC to examine it for vulnerabilities, then worked with another researcher, who prefers to remain anonymous and goes by the handle “Dora the SCADA explorer,” who wrote three exploits for vulnerabilities they found.
“Within three hours we had written a program to exploit the [Siemens] PLC we were testing,” said Rad, noting that it cost them just $2,500 to acquire everything they needed to research the vulnerabilities and develop the exploits. More
Thursday, July 28, 2011
Scotland Yard Busts Suspected LulzSec Spokesman

The London Metropolitan Police on Wednesday arrested a 19-year-old Shetland Islands man who they say is “Topiary,” the most visible figure in LulzSec.
LulzSec’s leader, “Sabu,” remained active on Twitter Wednesday morning, but did not immediately acknowledge the arrest of his purported frontman. More
Labels:
computer crime,
hackers,
hacking,
lulzsec,
scotland yard busts suspected lulzsec spokesman,
tech news
Wednesday, July 20, 2011
FBI arrests 16 in Anonymous hacking investigation
CNET - Sixteen people were arrested in the United States today in connection with hacking attacks by the Anonymous group of online activists, as well as one person in the U.K. and four people in the Netherlands, the U.S. Department of Justice said.
An indictment filed last week in San Jose, Calif., names 14 people accused of conspiring to intentionally damage protected computers at PayPal last December in retribution for PayPal suspending WikiLeaks' account to prevent supporters from donating to the whistleblower site. The arrests were made in Alabama, Arizona, California, Colorado, the District of Columbia, Florida, Massachusetts, Nevada, New Mexico, and Ohio, the Justice Department said. The defendants were expected to make initial appearances throughout the day in federal courts in their areas.
In two other separate indictments, a Sarasota, Fla., man was arrested on charges of intentionally damaging a protected computer for allegedly accessing the Web site of InfraGard Tampa Bay, an FBI partner, in June. The complaint alleges that he released instructions on how to exploit the Web site.
Another man was arrested in Las Cruces, N.M., for allegedly stealing confidential business information from AT&T servers and posting it publicly in April. The defendant, who works as a customer support contractor for AT&T at outsource provider Convergys, is charged with accessing a protected computer without authorization for allegedly downloading thousands of documents, applications, and other files and then posting them on the Internet, the indictment says. The LulzSec hacking group publicized the release of those documents on June 25, according to the filing. More
An indictment filed last week in San Jose, Calif., names 14 people accused of conspiring to intentionally damage protected computers at PayPal last December in retribution for PayPal suspending WikiLeaks' account to prevent supporters from donating to the whistleblower site. The arrests were made in Alabama, Arizona, California, Colorado, the District of Columbia, Florida, Massachusetts, Nevada, New Mexico, and Ohio, the Justice Department said. The defendants were expected to make initial appearances throughout the day in federal courts in their areas.
In two other separate indictments, a Sarasota, Fla., man was arrested on charges of intentionally damaging a protected computer for allegedly accessing the Web site of InfraGard Tampa Bay, an FBI partner, in June. The complaint alleges that he released instructions on how to exploit the Web site.
Another man was arrested in Las Cruces, N.M., for allegedly stealing confidential business information from AT&T servers and posting it publicly in April. The defendant, who works as a customer support contractor for AT&T at outsource provider Convergys, is charged with accessing a protected computer without authorization for allegedly downloading thousands of documents, applications, and other files and then posting them on the Internet, the indictment says. The LulzSec hacking group publicized the release of those documents on June 25, according to the filing. More
Tuesday, July 19, 2011
Hacker Collective Anonymous to Launch Social Networking Site

Anonymous, which has claimed credit for several high-profile cyber attacks in recent months, plans to launch what it says will be a new social networking site called AnonPlus.
The group's move was apparently spurred by Google's decision to shut down Anonymous' Google+ account for community standard violations, a report by Mashable says.
For the moment, at least, AnonPlus appears to be little more than a single, somewhat poorly formatted page that seeks to explain what the site will be about.
"This lil info dump of a site is here simply to dispence (sic) info, soon the actual site will go up and you can begin to interact with it," a message on the site notes.
"This project is not overnight and will take many of those out there who simply want a better internet," the message noted. "We will not be stopped by those looking to troll or those willing to stop the spreading of the truth."
The message makes no mention of Google shutting down Anonymous' Google+ account, but it does promise members that with AnonPlus there would be no fear of "censorship", "blackout" or "holding back." It goes on to add that the site is open to anyone who cares to join and not just to members of Anonymous.
It will be interesting to see if the effort gains any traction at all. Anonymous, which prefers being referred to as a collective rather than a group, has been in the news recently for several attacks against high-profile targets.
Background
Most recently, Anonymous claimed credit for an attack against military contractor Booz Allen Hamilton that resulted in the compromise of 90,000 email addresses and passwords belonging to military personnel. More
Subscribe to:
Comments (Atom)




